
Seal Software and the Duke Law AI Showdown: Real-life Validation of #TheRealThing
By Jim Wagner, Chief Strategy Officer at Legal AI company Seal Software
A few weeks ago, I read an article from the MIT Technology Review that highlighted the challenge that enterprises confront when trying to assess the value and validity of claims by AI vendors.
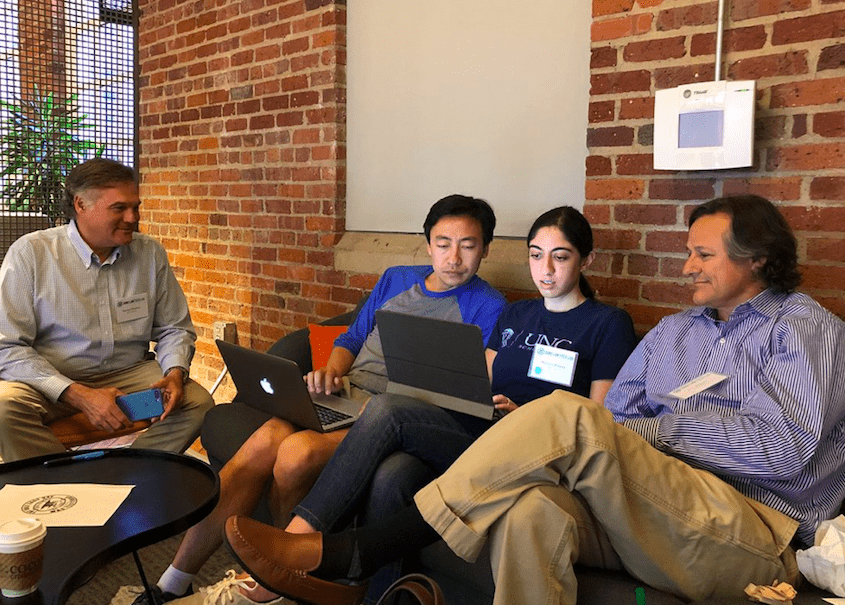
At the invitation of Duke Law professor, Jeff Ward, last week Steve Harber and I, along with our Seal Software colleagues, Scott Ripps and Ian Walker, had the pleasure of collaborating with the Duke Center on Law and Technology, and law school students from Duke, UNC and Wake Forest, to test just how effective real AI can be for the analysis of thousands of corporate contracts in just a few hours. Here’s what we did.
On Thursday evening, last week, we held a brief training session to teach the students how to use the Seal Software platform to create AI-based models to analyze contracts. The next morning, we brought together the teams from Duke, UNC and Wake Forest and gave them a real-life fact pattern, confronting complex legal issues related to data breaches, limitations of liability and cyber protections, and a clean Seal environment to solve their problems.
After giving the teams their fact pattern, we ‘turned them loose’ in Seal and gave them four hours and free reign to create AI analytics. Here’s the fact pattern we gave the students … and for those of you who have spent time as a 1L being grilled by your contracts professor, take comfort in the fact that there were no blue books required … just a login to Seal.

The Facts:
- You are the associate general counsel of a publicly traded pharmaceutical company. Yesterday, you were notified that one of your vendors was hacked a month ago, exposing not only their data, but also the data of your company and your clinical trials participants. When you looked at the supplier’s agreement, you discovered that the supplier’s liability was limited to $5 million dollars. You also discovered that there was no requirement that the supplier maintain cyber insurance. Also, your boss, the general counsel of the company, now is asking why the supplier didn’t notify you of the breach sooner.
- The general counsel is outraged with your findings for the supplier who was hacked and now wants a report by two pm today on as many of the following topics as possible:
- Is there a requirement in your contracts that the suppliers must indemnify you?
- Of your supplier agreements, how many contain a limitation of liability clause? What are the dollar caps for each limitation of liability clause?
- How many of your contracts include a specific requirement that the supplier maintain cyber insurance? Is there any way to determine the amount of cyber insurance required for each contract?
- Are your vendors required to provide notice of a data breach? If so, how many specify a time period within which notice has to be delivered?
Your challenge: use the Seal platform to build custom analytics to help research each of these topics
So how did the students do?
I never cease to be amazed by the talent – the intelligence, the decision making, the collaborative approach, and the enthusiasm – of the next generation of students. Simply stated, the legal professionals from Duke, UNC and Wake Forest were nothing short of awesome in how quickly they grasped the issues for analysis, and even more so how quickly they mastered the technology at their disposal to solve their problems.
In a four-hour period, the students created custom analytics from scratch using the Seal AI engine to analyze indemnification obligations, liability caps, cyber insurance requirements, and data breach notifications requirements.
Imagine trying to analyze 2,500 contracts in 4 hours for such a complex fact pattern – but that’s exactly what these young professionals did. The winning team from UNC, consisting of Mariam Badiei Turner, Rana Jamal Odeh, and Dean Yu, turned in an impressive array of analytics, not only identifying the relevant contractual clauses, but breaking them down in granular detail.
In particular, Mariam Turner from UNC ‘sealed’ the deal for her team, when she used every aspect of Seal’s AI to identify with specificity the time period within each supplier was required to provide notice of a data breach. We were all blown away.
We closed the AI Showdown by recognizing all of the law school participants, including the winning team, at the Duke Law Tech Lab demo day and awards ceremony. It was a great evening and a great way to finish the day.
Too often in a high-growth and demanding environment we don’t take time to step back and enjoy some of the little things – like spending time and giving back to a community that has given you so much (which the legal community, and Duke Law in particular, has given to me).
It’s also rare to have the opportunity to objectively observe what can be accomplished by combining the amazing intellect of bright and motivated students with a powerful AI platform like Seal to solve real-world problems. But the results from this effort were inspiring.
On behalf of myself and the entire Seal Software team, we would like to thank Jeff Ward, the Duke Law Tech Lab, and the students from Duke, UNC and Wake Forest, for their incredible level of enthusiasm and participation. It was a treat to spend time with such a talented group.
And back to that MIT article and how does it fit in to this story? As the saying goes, sometimes it’s hard to separate fact from fiction … especially so when it comes to the use of AI. When it came to the Duke AI Showdown, our group of energetic students showed to a certainty the power that a genuine AI platform can deliver.
#SealSoftware #TheRealThing
This is a sponsored thought leadership article by legal AI company, Seal Software
Discover more from Artificial Lawyer
Subscribe to get the latest posts sent to your email.
